5 September, 2018
On June 11, 2018, the National Information Security Standardization Technical Committee ("NISSTC") released a recommended national standard, the “Information Security Technology – Guide to Privacy and Security Impact Assessment” (Draft for Comment) (the "Draft for Comment"), in order to solicit opinions from the public by July 25, 2018.
I.What is “Privacy and Security Impact Assessment” (PSIA)?
To date, China's laws and regulations have not included any specific definition or application of the concept of privacy and security impact assessment. The concept of PSIA in a Chinese regulatory context was first mentioned on May 1, 2018 in the form of a recommended national standard, the “Information Security Technology – Personal Information Security Specification” (the “Specification”). In the Specification, PSIA was defined as referring to any personal information processing activities which test legal compliance levels, judge the risks to the legitimate rights and interests of personal information subjects, or evaluate the effectiveness of measures used to protect personal information subjects.
II.When is it necessary to conduct PSIA?
At present, there is no provision in the law as to how to conduct PSIA. Article 10.2 of the Specification stipulates that PSIA shall be conducted on a regular basis, that is at least once a year and that it should be re-evaluated in the following three situations: (1) new requirements in laws and regulations; (2) major changes in business models, information systems, operating environments; (3) major personal information security incidents.
The Draft for Comment provides further detail of certain situations requiring more extensive evaluation, such as:
- overseas transfer of personal information;
- changes to the purpose of personal information processing;
- prior to personal information being entrusted for processing, transfer, sharing or public disclosure; or changes to the scope of the above activities;
- assessment of the effect of anonymization and de-identification of personal information;
- re-identifying information that has been de-identified;
- collection of personal information through sales transactions or other means;
- collection of personal information using an “exception to consent rules” clause;
- collection of personal information using an “acquiescence consent” clause;
- prior to providing personal information to government, regulatory authorities, the judiciary;
- when there are users complaints and when disputes are not resolved.
III.What aspects require evaluation?
Article 10.2(b) of the Specification stipulates that any PSIA shall mainly assess the compliance of processing activities against the basic principles of personal information security, and also assess the impact of personal information processing activities on the legitimate rights and interests of personal information subjects, including but not limited to:
(a) Whether the collection of personal information follows the principles of clear purpose, acquiring consent, and data minimization;
(b) Whether the processing of personal information might adversely affect the legitimate rights and interests of the personal information subjects, including whether it might endanger personal and property safety, damage personal reputation or physical and mental health, and lead to discriminatory treatment, and so on;
(c) The effectiveness of personal information security measures;
(d) The risk of re-identification of personal information subjects after data anonymization and de-identification;
(e) Any possible adverse effects on the legitimate rights and interests of personal information subjects due to sharing, transferring, or publicly disclosing personal information;
(f) Any possible adverse effects on the legal rights and interests of personal information subjects when security incidents occur.
The Draft for Comment indicates the types of evaluation content that should be emphasized, in various evaluation situations. For example, for an impact assessment prior to a change of the purpose for personal information processing, the Draft for Comment proposes that key elements should include:
(a) A reasonable understanding of the original purpose of collecting the personal information and the manner and method of processing personal information;
(b)The circumstances in which personal information is collected, including the relationship between the subject of personal information and the controller of personal information, the scope of goods or services, trademarks and names used, the way in which the personal information is used by the subject, or the convenience provided by goods or services with personal information subjects;
(c) The manner in which personal information can be reasonably expected to be treated in a particular situation, taking into account considerations such as: the types of personal information that will be likely to be required in the course of normal business operations; the range, frequency, nature, and history of direct interaction between subjects of personal information; the type of personal information that will be likely to be required for the purposes of providing goods or services, or for improving or promoting goods or services.
IV.How to conduct PSIA?
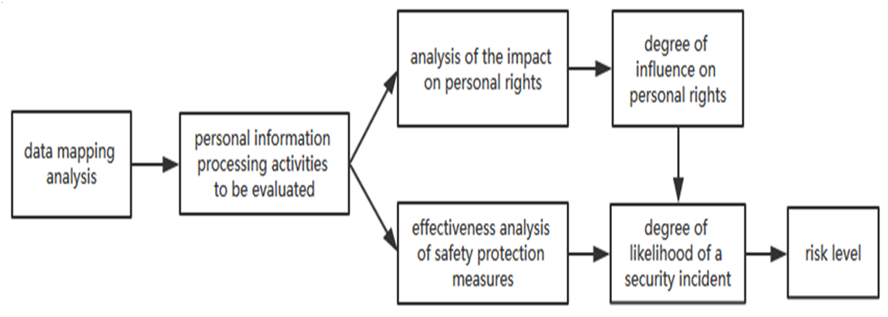
The Draft for Comment uses the following flow chart to summarize the principles of assessment.
Please click on the image to enlarge.
The evaluation methods recommended in the Draft for Comment are primarily interviews, inspections and tests.
- Interview refers to talking with relevant personnel of the information system in order to find and analyze the design and actual content of personal information protection measures in the information system;
- Inspection refers to observation, inspection and analysis of management systems, and any agreements, documents, and operational records;
- Test refers to test access control, identity verification, security audit mechanisms, event response capabilities, and so on.
V.Our observations
Although current laws and regulations do not mandate PSIA as a prerequisite for collecting and processing personal information, in practice, in the interests of corporate compliance, some companies are already implementing elements of PSIA in their internal data management processes. The EU General Data Protection Regulation (GDPR), which came into effect on May 25, 2018, also stipulates that if a data processing method, especially one that uses new technologies to process data, is likely to pose a serious risk to the rights and freedoms of natural persons, it should take into account the nature, scope, content and purpose of the data processing, and the method should be evaluated before data is processed. In practice, through the course of PSIA, it should be possible to the comprehensively analyze and evaluate the entire process of data collection, thereby assisting companies to determine whether data can be collected, the most effective way to save and process data, and how to control any risks associated with data collection. If the Draft for Comment should be formally issued, it will not constitute a mandatory legal obligation, but will provide a useful reference for evaluation of a company's PSIA practice.

.jpg)